Whitepixel breaks 28.6 billion password/sec
09 Dec 2010
Keywords: amd attack bruteforcing gpu hardware performance
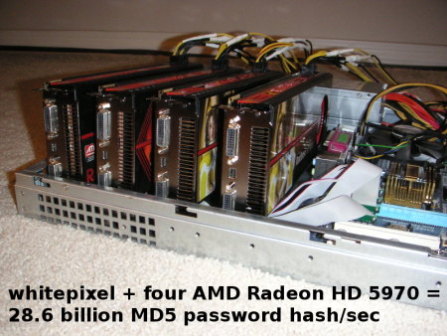
I am glad to announce, firstly, the release of whitepixel, an open
source GPU-accelerated password hash auditing software for AMD/ATI graphics
cards that qualifies as the world's fastest single-hash MD5 brute forcer; and
secondly, that a Linux computer built with four dual-GPU AMD Radeon HD 5970
graphics cards for the purpose of running whitepixel is the first demonstration
of eight AMD GPUs concurrently running this type of cryptographic workload on a
single system. This software and hardware combination achieves a rate of 28.6
billion MD5 password hashes tested per second, consumes 1230 Watt at full load,
and costs 2700 USD as of December 2010. The capital and operating costs of such
a system are only a small fraction of running the same workload on Amazon EC2
GPU instances, as I will detail in this post. [Update 2010-12-14: whitepixel v2 achieves a higher rate of 33.1 billion password/sec on 4xHD 5970.]
Software: whitepixel
See the whitepixel project page for more information, source code, and documentation.Currently, whitepixel supports attacking MD5 password hashes only, but more hash types will come soon. What prompted me to write it was that sometime in 2010, ATI Catalyst drivers started supporting up to 8 GPUs (on Linux at least) when previously they were limited to 4, which made it very exciting to be able to play with this amount of raw computing performance, especially given that AMD GPUs are roughly 2x-3x faster than Nvidia GPUs on ALU-bound workloads. Also, I had previously worked on MD5 chosen-prefix collisions on AMD/ATI GPUs. I had a decent MD5 implementation, wanted to optimize it further, and put it to other uses.
Overview of whitepixel
- It is the fastest of all single-hash brute forcing tools: ighashgpu, BarsWF, oclHashcat, Cryptohaze Multiforcer, InsidePro Extreme GPU Bruteforcer, ElcomSoft Lightning Hash Cracker, ElcomSoft Distributed Password Recovery.
- Targets AMD HD 5000 series and above GPUs, which are roughly 2x-3x faster than high-end Nvidia GPUs on ALU-bound workloads.
- Best AMD multi-GPU support. Works on at least 8 GPUs. Whitepixel is built directly on top of CAL (Compute Abstract Layer) on Linux. Other brute forcers support fewer AMD GPUs due to OpenCL libraries or Windows platform/drivers limitations.
- Hand-optimized AMD IL (Intermediate Language) MD5 implementation.
- Leverages the bitalign instruction to implement rotate operations in 1 clock cycle.
- MD5 step reversing. The last few of the 64 steps are pre-computed in reverse so that the brute forcing loop only needs to execute 46 of them to evaluate potential password matches, which speeds it up by 1.39x.
- Linux support only.
- Last but not least, it is the only performant open source brute forcer for AMD GPUs. The author of BarsWF recently open sourced his code but as shown in the graphs below it is about 4 times slower.
To compile and test whitepixel, install the ATI Catalyst Display drivers (I have heavily tested 10.11), install the latest ATI Stream SDK (2.2 as of December 2010), adjust the include path in the Makefile, build with "make", and start cracking with "./whitepixel $HASH". Performance-wise, whitepixel scales linearly with the number of GPUs and the number of ALUs times the frequency clock (as documented in this handy reference from the author of ighashgpu).
http://blog.zorinaq.com/whitepixel-breaks-286-billion-passwordsec/

No comments:
Post a Comment